 CLICK HERE TO DOWNLOAD THIS IMAGE & COLOR IT IN!
CLICK HERE TO DOWNLOAD THIS IMAGE & COLOR IT IN!Inside: A rallying call for Facilitator feedback as we design Ally’s TTX scenario generation engine, dispatches from the field to inspire your next exercise, and a look behind the curtain at the proving grounds where Ally’s platform enhancements earn the mark of quality.

We’ve got our noses to the grindstone as we forge our next legendary tool for Facilitators: the long-requested scenario generation engine. However, we don’t want to craft this epic piece in a bubble. This is our rallying call for feedback from fellow cybersecurity guildmates!
When you pick up the quill to draft out a TTX scenario, where do you start? What discovery questions do you need answered to map out the scenario’s journey? What visibility spells do you pull from your grimoire when info is limited and you need a reliable method for cutting through the fog?
We’ve held internal council and collected thoughts of our own, but we’re eager to hear the battle-tested wisdom that you’ve gained in the field. For example, I discovered this WEF Global Cybersecurity Outlook scroll during a recent research delve and would love to know if you’ve found similar treasures in your own adventures:
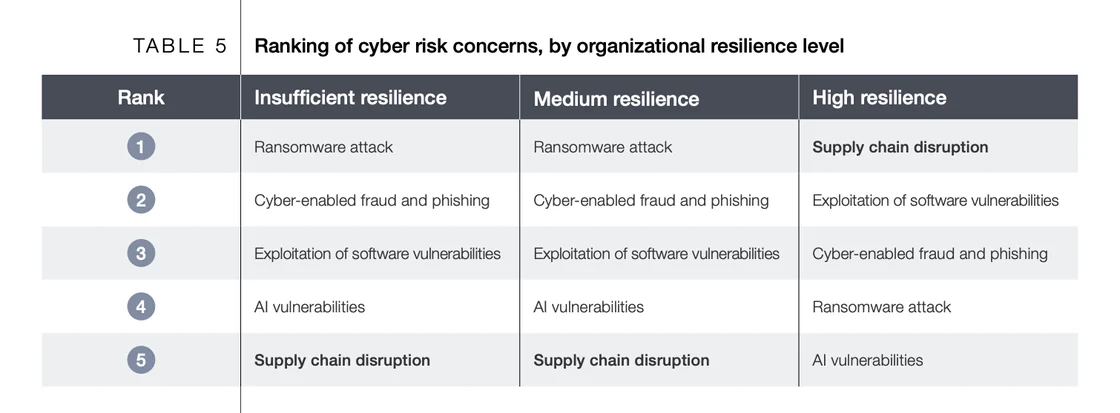
Every great scenario is based on the shape and state of the kingdom you’re defending. During the TTX planning phase, does organizational maturity determine the difficulty of the foes you summon? Do resilience levels dictate whether you test the walls…or the throne room itself? These are the quiet judgments Facilitators make before the first die is ever cast, and they’re the wisdom we want to honor as we fashion this new engine.
Email rob@ally.security and let us know!
Your allies in IR,
Rob & Scout


A trove of scraped Instagram account data now circulates in the Shadowfell, offering phishers fresh names and contact info. For Facilitators, it's a clear lesson that seemingly modest disclosures can arm tricksters with a new arsenal of dastardly tools. Read the field report
One patient adversary known as Zestix/Sentap deftly traded stolen credentials to hackers like skeleton keys in a shadow market. For Facilitators, it is a potent reminder that many great breaches begin not with siege engines, but with a single unlocked door. Discover what happened
New cyber laws march ever-closer, expanding reporting duties and tightening expectations across supply chains and critical services. For Facilitators, it prophesizes a future where regulation itself becomes a scenario driver, especially when crown jewels are at stake. Unfurl the legal scroll
A sweeping global survey reveals that when cyber strikes land, many enterprises remain hobbled for weeks, not days, as recovery grinds on behind the scenes. For Facilitators, it is a reminder that resilience is proven not only during the breach, but in the long march of recovery that follows. Unlock the intel

Before we hand a new tool to our users, it must first survive the proving ground. Here, strength is measured under strain to ensure a well-tempered, solid experience. When we construct new capabilities for the Ally platform, it must survive the following two trials before being released into the open world:
Together, these proving grounds shape what ultimately reaches production. The result is a platform tested by both automatons and people, ready to serve Facilitators with confidence when it matters most. Once a tool leaves the proving ground, it bears the mark of quality.


We’ve walked the proving ground where new Ally enhancements earn their stripes and charted fresh intelligence from the field. With that, your satchel should be well-stocked for the next scenario you bring to life.
Before you set off on your next grand campaign, don’t forget to hit reply and share how you build your TTX scenarios. We’d love to slot your feedback into our new scenario generation tool!
About Ally Security
Ally is here to support facilitators, which in turn creates a virtuous cycle where exercises take less time, provide more value, are run more frequently, and can make every organization can be better prepared.
The unexpected wins. The client curveballs. The chaos you couldn’t have scripted if you tried. Dear Asa is your space to share the stories that don’t make it into the official post-incident report. Script, submit, and enjoy a chance to be featured or quoted in an upcoming post.
